3 2 B 2 2 7b
Greels
Apr 03, 2025 · 5 min read
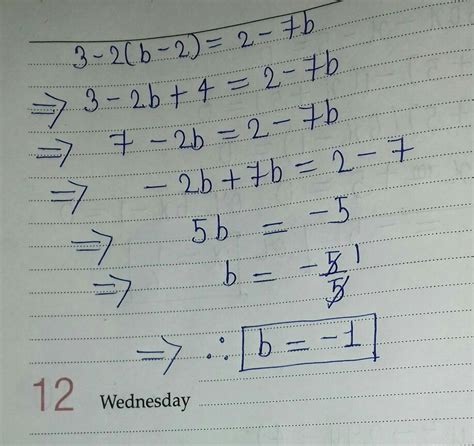
Table of Contents
Decoding the Enigma: A Deep Dive into "3 2 b 2 2 7b"
The seemingly innocuous string of characters, "3 2 b 2 2 7b," has captivated the internet, sparking countless discussions and theories. Is it a code? A cryptic message? A random sequence? This article will explore the possibilities, analyze its structure, and delve into the various interpretations that have emerged. We'll examine its potential connections to different fields, from mathematics and cryptography to linguistics and even the more esoteric realms of numerology.
Unraveling the Mysteries: Potential Interpretations
The first step in deciphering "3 2 b 2 2 7b" is to identify potential patterns and underlying structures. The presence of both numbers and letters immediately suggests a system involving a combination of numerical and alphabetical components.
1. A Numerical Cipher:
One of the simplest interpretations involves viewing the string as a numerical cipher. The numbers 3, 2, 2, 2, and 7 could represent positions in an alphabet, a specific codebook, or even coordinates within a particular system. The letters 'b' could be placeholders, separators, or indicators of operational changes within the cipher. However, without a key or further contextual clues, this approach remains highly speculative. Further analysis might involve:
- Frequency Analysis: Examining the frequency of each number and letter to look for potential biases or patterns.
- Modular Arithmetic: Exploring the application of modular arithmetic, where numbers are expressed as remainders after division by a fixed number (a modulus).
- Substitution Ciphers: Investigating whether the numbers and letters represent substitutions for other characters, based on a specific key or algorithm.
2. A Base Conversion System:
The string could represent a number written in a non-decimal base system. Base systems other than our familiar base-10 (decimal) system exist, such as binary (base-2), ternary (base-3), hexadecimal (base-16), and so on. The presence of the letter 'b' could be a deliberate inclusion, perhaps indicating a change in base or a specific element in the sequence. This approach requires exploring various bases to see if a meaningful representation emerges. Consider:
- Trial and Error: Testing various base systems to see if the string translates into a recognizable value or pattern.
- Pattern Recognition: Observing if the sequence follows a mathematical progression or pattern within a specific base system.
- Mathematical Relationships: Investigating the numerical relationships between the components of the string within different base systems.
3. A Linguistic or Alphabetical Code:
The inclusion of letters opens up the possibility of a code operating on an alphabetical system. The numbers could represent specific word positions, letter shifts, or even represent syllables or phonemes. Several scenarios are possible:
- A Caesar Cipher: This classic cipher involves shifting each letter a certain number of positions down the alphabet. However, the presence of numbers complicates its direct application here.
- A Keyword Cipher: A keyword cipher utilizes a keyword to encrypt the message, scrambling the letters based on their positions in the alphabet relative to the keyword. The numbers might relate to the keyword's position or the positions of letters within the encrypted message.
- A Polyalphabetic Cipher: This more complex method employs several different Caesar ciphers, switching between them during the encryption process, leading to more secure messages.
4. A Combination Approach:
The most likely scenario is that "3 2 b 2 2 7b" represents a combination of the methods discussed above. It's possible the string utilizes a hybrid system blending numerical and alphabetical codes, perhaps with layered encryption. This would require:
- Careful Deconstruction: Breaking the string into smaller, more manageable segments.
- Identifying Patterns: Looking for recurring sequences or patterns within the numbers and letters.
- Iterative Testing: Testing different combinations of methods, gradually refining the decoding approach based on the results.
Beyond Simple Codes: Exploring Broader Interpretations
The analysis shouldn't be limited to pure cryptography. Consider the possibility that "3 2 b 2 2 7b" functions as a symbolic representation or a reference to a specific context.
5. Mathematical or Geometric Relationships:
The numbers might represent dimensions, coordinates, or elements within a mathematical or geometric system. It could represent a point in space, an equation, or even a sequence within a mathematical pattern. Further investigation should include:
- Geometric Plotting: Exploring whether the numbers correspond to points on a plane or in three-dimensional space.
- Mathematical Sequences: Analyzing the numbers to see if they form part of a known mathematical sequence (e.g., Fibonacci, arithmetic progression).
- Equations and Formulas: Trying to fit the numbers into mathematical equations or formulas to uncover any meaningful relationships.
6. A Reference to External Sources:
The string might be a reference to something external, such as:
- A Book or Text: Certain page numbers, chapter references, or specific word positions could be indicated by the combination of numbers and letters.
- A Piece of Music: Musical notation sometimes uses numbers to represent notes or rhythms.
- A Computer Program: The string might represent a part of a program code, indicating a specific line or function.
7. A Random Sequence:
Finally, we must consider the possibility that "3 2 b 2 2 7b" is simply a random sequence of characters. While this is a less exciting possibility, it's important to consider as a baseline for comparison when evaluating the other interpretations. Statistical analysis could help determine the probability of the string being randomly generated.
Advanced Techniques and Further Exploration
Advanced techniques for decryption could include:
- Computer Algorithms: Developing computer algorithms to automate the testing of different decryption methods.
- Machine Learning: Using machine learning models to analyze patterns and identify potential connections in the string.
- Expert Consultation: Seeking advice from cryptographers, mathematicians, linguists, or other relevant experts.
The Importance of Context:
The key to deciphering "3 2 b 2 2 7b" likely lies in obtaining more context. Where did you encounter this string? What was the surrounding conversation or situation? Any additional information could significantly aid in its interpretation.
Conclusion: The Ongoing Quest for Meaning
The enigma of "3 2 b 2 2 7b" remains an intriguing puzzle. While definitive conclusions are currently elusive, this article presents a comprehensive framework for approaching its deciphering. The exploration encompasses multiple fields of study, highlighting the interdisciplinary nature of code-breaking and the potential for unexpected connections. Further investigation, utilizing both manual analysis and advanced techniques, promises to unravel this captivating mystery, demonstrating the power of human curiosity and the boundless possibilities of cryptic communication. The journey, rather than the destination, highlights the enduring allure of codes and the joy of intellectual exploration. The search continues…
Latest Posts
Latest Posts
-
How Many Kilograms Are In 22 Pounds
Apr 04, 2025
-
How Many Kilos Is 132 Pounds
Apr 04, 2025
-
How Many Days Is 75 Days From Today
Apr 04, 2025
-
172 Cm Is How Many Inches
Apr 04, 2025
-
How Tall Is 2 06 Meters In Feet
Apr 04, 2025
Related Post
Thank you for visiting our website which covers about 3 2 B 2 2 7b . We hope the information provided has been useful to you. Feel free to contact us if you have any questions or need further assistance. See you next time and don't miss to bookmark.
